Introduction
In the realm of cybersecurity, zero-day exploits represent a persistent and elusive threat. These vulnerabilities, which attackers exploit before developers have a chance to patch them, pose significant risks to systems and data security. For developers and IT teams, the discovery of a zero-day means an immediate scramble to protect their systems. This urgency underscores the importance of timely patching, an essential practice in safeguarding enterprise environments from cyber attacks. Recently, the tech community has been abuzz with news regarding leaked vulnerabilities in various Microsoft products—a revelation that affects Microsoft Defender and endangers over a billion Windows users.
Background and Context
Microsoft Defender has long held a crucial role in enterprise security strategies, acting as the first line of defense against malware and other malicious threats. Its integration into business operations is designed to provide comprehensive protection with minimal impact on system performance. However, the emergence of zero-day vulnerabilities like those disclosed recently disrupts this equilibrium. Historically, zero-day exploits have seen a sharp increase in exploitation, causing many organizations to suffer data breaches and financial losses.
The recent disclosure has sparked varied reactions from Microsoft and the wider security community. Microsoft has committed to investigating and addressing these vulnerabilities, an assurance aimed at maintaining public trust. Meanwhile, security experts worldwide are urging caution and swift action to mitigate potential damage. Such vulnerabilities force a reconsideration of current security protocols, highlighting gaps that could be exploited by threat actors.
What Exactly Changed
The recent leaks revealed three specific vulnerabilities within Microsoft Defender: BlueHammer, RedSun, and UnDefend. BlueHammer, which has been identified as CVE-2026-33825, was patched onApril 14, 2026. However, both RedSun and UnDefend remain unpatched as of April 21, 2026. This leaves a critical window open for attackers, amplifying the urgency for developers to employ interim defensive mechanisms.
The timeline of these events unfolded rapidly, beginning with the initial discovery of BlueHammer on April 1, 2026. Shortly after, on April 10, 2026, RedSun and UnDefend were identified, drawing immediate concern from cybersecurity professionals. These vulnerabilities were publicly disclosed by April 17, 2026, a move that some experts critique for potentially hastening exploitation by malicious parties. The ongoing unpatched state of RedSun and UnDefend poses a significant challenge, with the potential for serious implications if exploited in the wild.
What This Means for Developers
For developers, these vulnerabilities equate to an elevated risk of unauthorized access and potential data breaches. The unpatched flaws could be exploited to gain entry into systems, compromising sensitive information. Developers are now tasked with identifying and implementing additional security measures, a pressing concern given the high stakes involved.
Moreover, malware infections could lead to severe operational disruptions. These disruptions risk not only immediate business processes but also long-term strategic initiatives, potentially setting back project timelines. Developers might consequently need to explore alternative antivirus solutions to safeguard against these vulnerabilities until Microsoft delivers comprehensive patches.
Impact on Businesses/Teams
The impact of these vulnerabilities varies significantly between startups and larger enterprises. For startups, limited resources can make it particularly challenging to address such vulnerabilities swiftly. A single successful cyber attack can lead to catastrophic data breaches, compromising not only customer trust but also the startup’s viability.
On the other hand, larger enterprises face elevated costs when implementing additional mitigation strategies. Though they may possess more resources than startups, the reputational damage from a security breach can be far-reaching. Enterprises are thus under pressure to adjust their IT security protocols and enhance response times to protect their infrastructures against active threats.
How to Adapt / Action Items
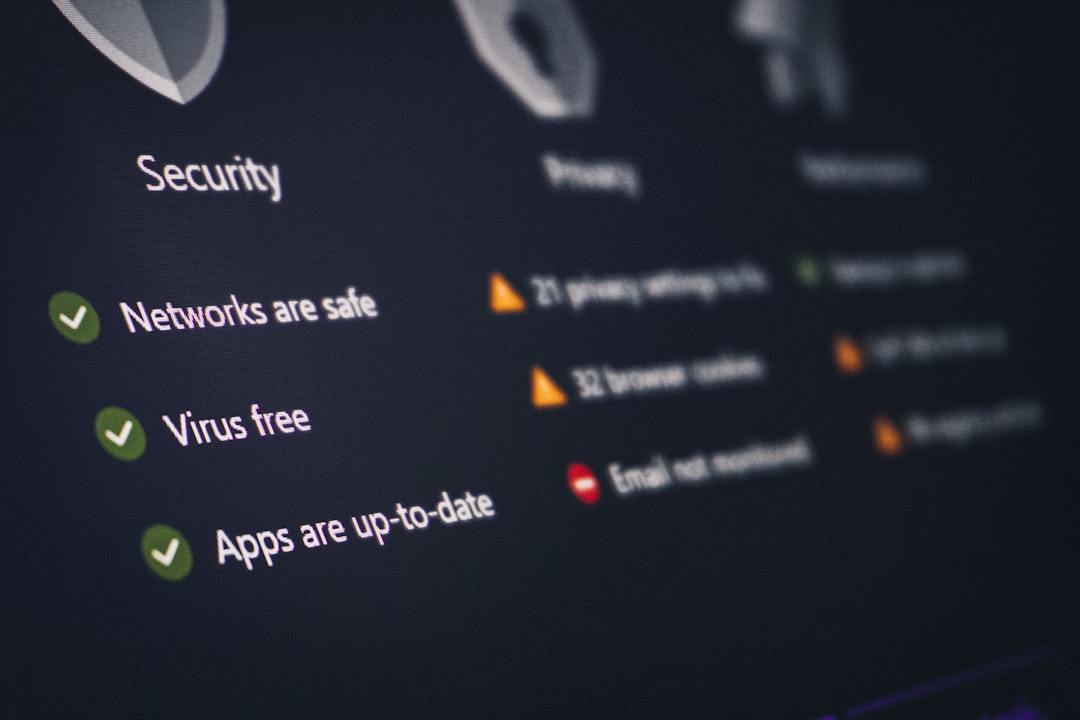
To mitigate these risks, IT security teams should immediately apply all available updates and patches. Keeping systems up to date remains a fundamental yet powerful defense against exploitation. Additionally, considering third-party antivirus solutions can provide an extra layer of security during this vulnerable period.
Active monitoring for exploitation signs is crucial. Utilizing advanced threat detection tools and real-time monitoring services can help teams identify unusual activities and respond swiftly. Developing an incident response plan specifically tailored for these network vulnerabilities is another recommended step to enhance readiness and mitigate potential impacts effectively.
Risks and Considerations
The unpatched state of RedSun and UnDefend introduces critical risks. Without patches, these vulnerabilities remain potential channels for unauthorized access and exploitation. Evaluating the likelihood of active exploitation must be a priority for IT teams, as overlooking this can lead to devastating cyber attacks.
User vigilance and proactive security measures become even more vital in this context. Teams should educate employees on recognizing phishing attempts and other tactics often used to exploit vulnerabilities. Ensuring robust security hygiene practices across the organization can further reduce the risk of successful exploitation attempts.
Conclusion
The disclosure of these zero-day vulnerabilities highlights a serious concern for systems relying on Microsoft technologies. The impact on user data and broader IT security frameworks is profound, emphasizing the necessity for enhanced communication and cooperation between tech firms and independent security researchers. Such collaboration is essential to developing timely solutions and preventing future incidents. Developers and enterprises alike are urged to remain vigilant and proactive in fortifying their security defenses against these evolving threats.